Posted by: TAZ Networks on August 28, 2020 at 12:00 pm
Every good business owner recognizes the need to properly secure their computer network. Firewalls, backups, and employee training are all necessary parts of this protection. But what about multi-factor authentication, or MFA? What is it, and how can it protect your computer network?
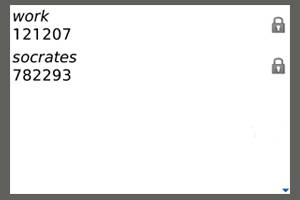
MFA, or multi-factor authentication software, will provide codes like this directly to your cell phone to help protect your network and comply with industry regulations.
What is Multi-Factor Authentication?
MFA is an additional protection for your network access. We’re all very familiar with user names and passwords. MFA is an additional security step beyond a password. First, the user enters their user name and password. Next, they receive a code via email or text message that they must enter to gain access to the network. This way, the code verifies the user before giving access to the network.
Multi-Factor Authentication Fights Phishing
One of the most common scams these days is phishing, where a hacker tries to get a user to give up their user name and password using a link to a fake site that looks very real. Once they have working credentials, the scammers can use them to log in to VPNs and other network components. From there, they can steal financial or other confidential records, or even install software that allows them continued access to the network any time they like, even if the company changes the original password.
With, MFA, however, the user whose credentials were stolen should get a text message or an email any time someone tries to use their user name and password. This should alert them and their IT department that their access credentials need to be changed immediately.
Multi-Factor Authentication and Compliance
Does your business have to comply with industry or governmental regulations? If your business is affected by compliance requirements, you must be able to demonstrate that all remote access is secure, even through a VPN. PCI, HIPAA and NIST all require some level of MFA for secure VPN access.
Interested in learning more about how multi-factor authentication can help protect your network, fight stolen credentials, and comply with regulations, including a fast and easy setup for Office 365? Contact TAZ Networks today for more information.
Image source and licensing information. Image has been modified from the original.