Posted by: TAZ Networks on May 5, 2017 at 3:27 pm
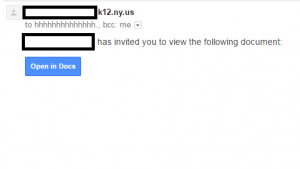
Screencap of the initial email from the Google Docs scam. Via Imgur.com
This week saw a massive Google Docs email scam that was particularly interesting for a couple of reasons:
- How widespread it was; and,
- How quick and widespread the warning and response were.
The first attack reports hit around 2:30 Wednesday afternoon.
We heard about it around 3:45, and sent out a quick Tweet and Facebook post.
By Wednesday evening, warnings were going out loud and clear over social media, sent by a wide variety of sources.
Why was the scam so widespread?
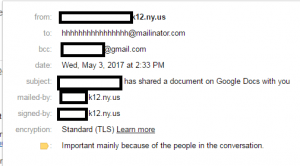
Screencap of the expanded sender details. Via Imgur.com
The scam acted much like a self-replicating “worm” virus. A worm’s main purpose is to infect as many computers as quickly as possible. So, once it has access to a user’s email account, it sends the same message to everyone in the contacts list. Since it was sending from real, infected users, all of the sending addresses were legitimate. It also looked very real, copying Google’s document-sharing invitation down to the letter.
Why was the warning so quick and widespread?
Oddly, one of the biggest groups the attacker chose to target was… journalists. People whose job it is to disseminate information to the public. So of course, once the more tech-savvy journalists realized what was happening, the media machine went into beast mode to get the word out.
Google also acted very quickly, shutting down the worm in less than an hour of the first reports. Still, in that timeframe, over 1 million Gmail users were affected.
What can we learn?
Not all email scams are easily identified by checking the sender information or content. Also check the “cc:” and “bcc:” fields. Who else was it sent to? (The hhhhhhhhhhhhhh@mailinator.com in the “to:” box still provides a good clue. Mailinator is a disposable email service.)
Specifically to Google app users, per Infosecurity Magazine, “Google Docs has account access by default and does not need to request extra permissions.” So requesting permission should have been a clue as well. However, not everyone is a regular user of Google Docs, so this could be easily missed.
Unfortunately, this kind of hacking attempt is likely to become more popular in the future. It puts a lot of pressure on Google to make sure their apps are legitimate, but a little “buyer beware” is always a good idea as well.