Posted by: TAZ Networks on November 9, 2018 at 8:00 am
What is Dharma Ransomware?
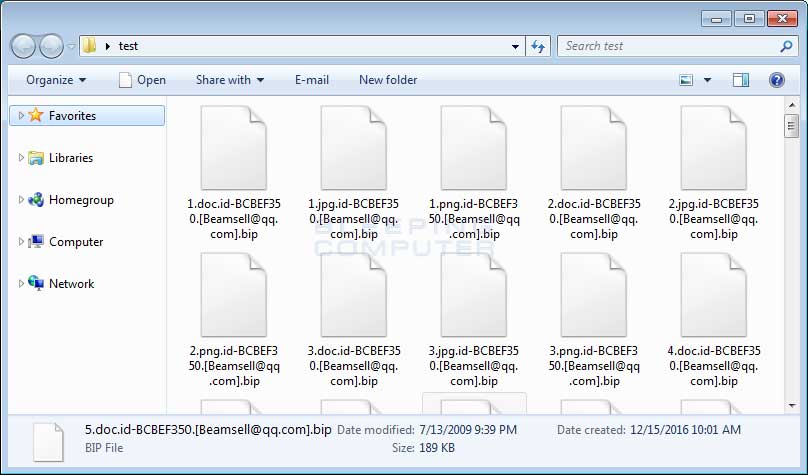
If your file extensions suddenly look like this, call us immediately. Image via BleepingComputer.com.
Dharma is what might be called a “true hack.” Rather than sneaking in through a malicious email link or attachment, Dharma infects your network by brute-force attack against Remote Desktop Services (RDS). This means that automated software rapidly sends multiple login attempts with different passwords to your RDS until it gets in.
(Of course, the hackers could also get in if an RDS password is leaked, which comes back to not clicking on those bad email links and attachments.)
Once in, the software starts encrypting files. Usually you can still see your file names, but now they might have a weird extension with an email address in it. (See example image.) Dharma deletes any “shadow copies,” making file restoration harder. The hackers then leave a ransom note with contact information.
If many files in the same folder suddenly have extensions you don’t recognize, call us immediately! Dharma also encrypts any new files created before the infection is removed.
We saw three slightly-different versions of Dharma attacks over the past few days. All three versions function the same way.
The good news: We identified and isolated the attacks in less than half an hour per instance. Since Dharma cannot be “de-encrypted”, we restored essential files from available backups.
How to Prevent Dharma Ransomware
- Use good, basic online security habits for passwords and attachments.
- Make sure all essential files and data are backed up before an attack. (This means now.)
- Don’t assume your Dharma attack can be decrypted.
- “Double-wall” your RDS. There are a few ways to do this that we’ll discuss below.
- Have a proactive attitude toward network security.
Here are details on each of these precautions:
Safe Online Habits: Make sure your entire staff is trained in — and uses — secure habits when online, such as not opening unexpected attachments, being aware of common email scams, and using complex passwords.
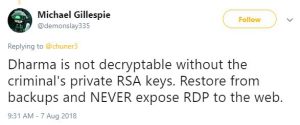
“Ransomware Hunter” Michael Gillespie discovered the “.combo” Dharma variant, which we encountered this week.
Backups: Are your essential business files backed up? Are you sure? How quickly can you restore a file? How old is the restored version? These are questions every business manager in charge of security should be able to answer.
Don’t Assume Decryption: Never assume a free “key” exists to unlock your files. While some of the older Dharma versions have free decrypters out on the internet), none of the new 2018 variants can be decrypted without paying. (And, wow, a lot of web sites out there claim they can unencrypt your files. Buyer beware.) The FBI recommends not paying if you can at all avoid it, since paying the hackers just funds future ransomware attacks.
The “Double-Wall”: Here are several ways to protect your RDS:
- Require users to log in though a VPN.
- Require complex, rotating passwords.
- Restrict access to only those who really need it.
- Implement multi-factor authentication.
As we step up security efforts on behalf of our clients, we get pushback every single time we implement one of these additional steps. Many of us remember when the internet was “easy” and “fun” with a lot fewer passwords to remember. It isn’t that way anymore (if it ever really was). Yes, using these precautions takes an extra few seconds to log in. However, implementing these additional protections are necessary to keep your business data safe. Which leads us to…
Attitude: Prevention is largely affected by the attitude of business decision makers. While basic end-user cybersecurity education is important, Dharma directly attacks servers that can be accessed by the internet, like RDS. Your staff doing the day-to-day work of your business can’t – and probably shouldn’t – make decisions about password policies and backups. Therefore, it’s essential that business decision makers are willing to properly secure company servers.
Need help? TAZ Networks offers a range of business network security services to help SMB owners and managers properly secure their critical business data. Contact us today for more information.